
1. In terms of the level of the operating system, Windows XP is still a C-level operating system, that is to say, it is an operating system with a relatively low security level. The other side of the security of the operating system depends on whether there are many vulnerabilities as software, which allows hackers to take advantage of it.
2. WindowsXP can use audit to track user accounts used to access files or other objects, login attempts, system shutdown or restart, and similar events, and auditing files and folders under NTFS partitions can ensure the security of files and folders.
3. AnFull template is a file representation that can define security policies. It can configure the security settings of accounts and local policies, event logs, restricted groups, file systems, registries, system services and other items. Security templates exist in text files in .inf format, and users can conveniently copy, paste, import or export some templates.
4. DEP (Data Execution Prevention) means "data execution protection", which is a security mechanism of Windows, which is mainly used to prevent viruses and other security threats from damaging the system.

1. A healthy ecosystem is the material basis for human survival and development, as well as the basis of human health. Maintaining and maintaining the sustainability of the structure and function of the ecosystem, repairing the wounds of the ecosystem, rebuilding the destroyed earth's life support system, and achieving ecosystem health are important tasks for environmental workers and environmental management departments in the future.
2. The foundation of health depends on a person's lifestyle and personal habits.A healthy foundation requires people to adhere to healthy eating habits, such as eating more vegetables, fruits and coarse grains, and less greasy food and high-calorie drinks. In addition, sticking to exercise is also a necessary condition for having a healthy foundation.
3. Social stability, economic development, medical and health conditions have improved significantly. Since the founding of the People's Republic of China, especially since the reform and opening up, China has made remarkable achievements in the reform and development of the field of health, and the people's health level has been continuously improved.
4. The basis of a person's good health is to maintain a happy mood, have a positive attitude, strengthen physical exercise, increase resistance, have a regular routine, combine work and leisure, quit smoking and drink less, maintain health care, etc. These are the foundations of physical health.
1. Models of virtual A/B update mechanism: At present, the model of virtual A/B that adopts the new update mechanism of the Android system can be suspended during the download process of downloading the new version of the system. Click the download progress bar to suspend the download.
2. The newly upgraded OriginOS 3 brings many new features and new functions such as "in-situ resurrection mechanism, large folder icon mode, super-small window multitasking, intelligent sidebar, zero-pressure focus mode", bringing users a smooth, easy-to-use and highly designed system experience.
3. iQOO can't be upgraded because of root (obtaining the highest permission). The mobile phone after root cannot be officially upgraded directly, but the official (new) version of the line brush package can be flashed. After brushing (upgrade), root.If you have tried it and it still doesn't work, it is recommended to bring the purchase invoice to the after-sales maintenance office for maintenance.
How to track compliance breaches-APP, download it now, new users will receive a novice gift pack.
1. In terms of the level of the operating system, Windows XP is still a C-level operating system, that is to say, it is an operating system with a relatively low security level. The other side of the security of the operating system depends on whether there are many vulnerabilities as software, which allows hackers to take advantage of it.
2. WindowsXP can use audit to track user accounts used to access files or other objects, login attempts, system shutdown or restart, and similar events, and auditing files and folders under NTFS partitions can ensure the security of files and folders.
3. AnFull template is a file representation that can define security policies. It can configure the security settings of accounts and local policies, event logs, restricted groups, file systems, registries, system services and other items. Security templates exist in text files in .inf format, and users can conveniently copy, paste, import or export some templates.
4. DEP (Data Execution Prevention) means "data execution protection", which is a security mechanism of Windows, which is mainly used to prevent viruses and other security threats from damaging the system.

1. A healthy ecosystem is the material basis for human survival and development, as well as the basis of human health. Maintaining and maintaining the sustainability of the structure and function of the ecosystem, repairing the wounds of the ecosystem, rebuilding the destroyed earth's life support system, and achieving ecosystem health are important tasks for environmental workers and environmental management departments in the future.
2. The foundation of health depends on a person's lifestyle and personal habits.A healthy foundation requires people to adhere to healthy eating habits, such as eating more vegetables, fruits and coarse grains, and less greasy food and high-calorie drinks. In addition, sticking to exercise is also a necessary condition for having a healthy foundation.
3. Social stability, economic development, medical and health conditions have improved significantly. Since the founding of the People's Republic of China, especially since the reform and opening up, China has made remarkable achievements in the reform and development of the field of health, and the people's health level has been continuously improved.
4. The basis of a person's good health is to maintain a happy mood, have a positive attitude, strengthen physical exercise, increase resistance, have a regular routine, combine work and leisure, quit smoking and drink less, maintain health care, etc. These are the foundations of physical health.
1. Models of virtual A/B update mechanism: At present, the model of virtual A/B that adopts the new update mechanism of the Android system can be suspended during the download process of downloading the new version of the system. Click the download progress bar to suspend the download.
2. The newly upgraded OriginOS 3 brings many new features and new functions such as "in-situ resurrection mechanism, large folder icon mode, super-small window multitasking, intelligent sidebar, zero-pressure focus mode", bringing users a smooth, easy-to-use and highly designed system experience.
3. iQOO can't be upgraded because of root (obtaining the highest permission). The mobile phone after root cannot be officially upgraded directly, but the official (new) version of the line brush package can be flashed. After brushing (upgrade), root.If you have tried it and it still doesn't work, it is recommended to bring the purchase invoice to the after-sales maintenance office for maintenance.
Predictive analytics for trade flows
author: 2024-12-24 00:16Livestock products HS code classification
author: 2024-12-23 23:09HS code-driven margin analysis
author: 2024-12-23 22:15How to utilize blockchain for trade
author: 2024-12-23 21:57Global trade content syndication
author: 2024-12-23 21:56International trade database customization
author: 2024-12-24 00:25Export data analysis for consumer goods
author: 2024-12-24 00:12Cocoa and chocolate HS code insights
author: 2024-12-23 23:55Industry reports segmented by HS code
author: 2024-12-23 23:52HS code-led regulatory frameworks
author: 2024-12-23 22:14 Comparative freight cost modeling
Comparative freight cost modeling
897.36MB
Check HS code-based trade route profitability
HS code-based trade route profitability
953.61MB
Check How to detect illicit trade patterns
How to detect illicit trade patterns
271.22MB
Check International procurement intelligence
International procurement intelligence
829.19MB
Check HS code-based scenario planning for exports
HS code-based scenario planning for exports
628.14MB
Check Customizable shipment reports
Customizable shipment reports
828.77MB
Check Global trade data for PESTEL analysis
Global trade data for PESTEL analysis
446.25MB
Check HS code-based opportunity scanning
HS code-based opportunity scanning
481.14MB
Check HS code consulting for exporters
HS code consulting for exporters
866.36MB
Check How to comply with global trade regulations
How to comply with global trade regulations
751.36MB
Check Ready-to-eat meals HS code classification
Ready-to-eat meals HS code classification
238.74MB
Check International trade knowledge base
International trade knowledge base
677.45MB
Check How to identify emerging market suppliers
How to identify emerging market suppliers
655.36MB
Check How to comply with EU trade regulations
How to comply with EU trade regulations
154.72MB
Check HS code research for EU markets
HS code research for EU markets
846.59MB
Check Real-time trade data feeds
Real-time trade data feeds
454.42MB
Check Export subsidies linked to HS codes
Export subsidies linked to HS codes
695.48MB
Check Non-tariff barriers by HS code
Non-tariff barriers by HS code
592.24MB
Check HS code strategies for trade diversification
HS code strategies for trade diversification
629.81MB
Check Advanced HS code product classification
Advanced HS code product classification
111.13MB
Check Timber and wood products HS code trends
Timber and wood products HS code trends
495.35MB
Check Global import export data subscription
Global import export data subscription
364.79MB
Check How to use trade data in negotiations
How to use trade data in negotiations
486.68MB
Check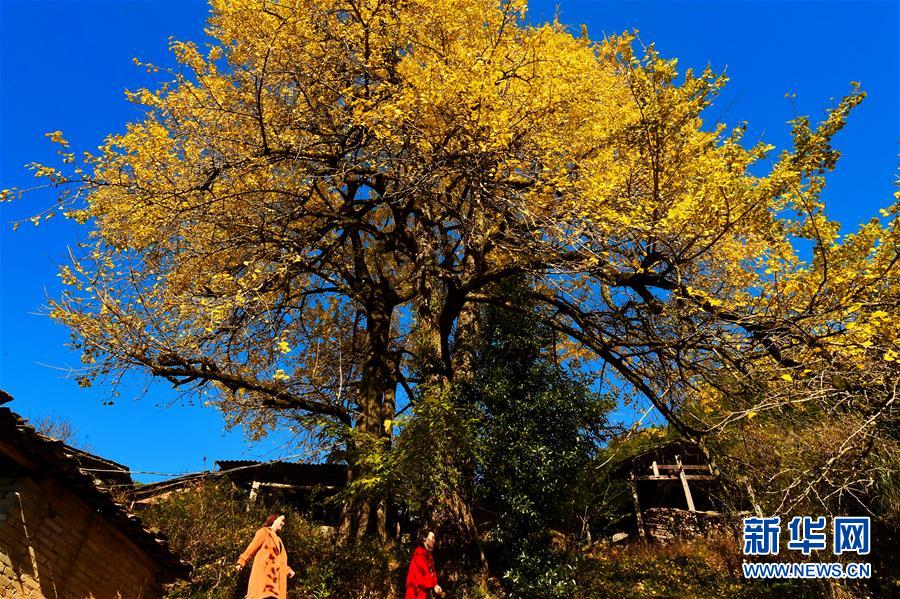 international suppliers data
international suppliers data
732.63MB
Check Trade compliance training resources
Trade compliance training resources
729.28MB
Check How to align sourcing strategy with trade data
How to align sourcing strategy with trade data
982.55MB
Check Trade intelligence for marine cargo
Trade intelligence for marine cargo
484.65MB
Check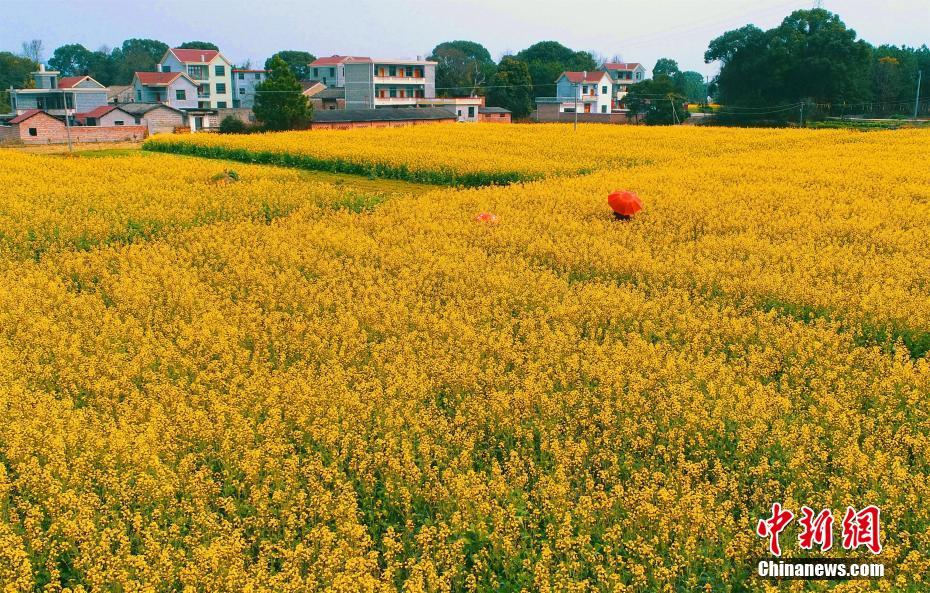 Trade data integration with BI tools
Trade data integration with BI tools
774.54MB
Check Trade data solutions for freight forwarders
Trade data solutions for freight forwarders
264.53MB
Check Chemical HS code alerts in EU markets
Chemical HS code alerts in EU markets
637.73MB
Check Global cross-border payment tracking
Global cross-border payment tracking
361.87MB
Check Optimizing tariff schedules by HS code
Optimizing tariff schedules by HS code
331.36MB
Check HS code guides for automotive parts
HS code guides for automotive parts
336.84MB
Check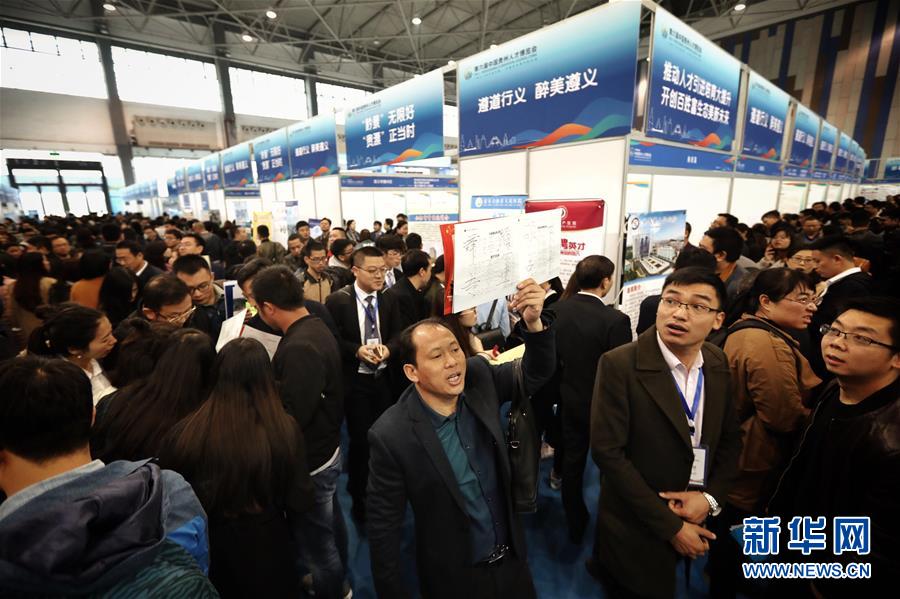 How to use data for HS code classification
How to use data for HS code classification
377.17MB
Check How to understand INCOTERMS with data
How to understand INCOTERMS with data
495.19MB
Check Real-time cargo tracking solutions
Real-time cargo tracking solutions
276.84MB
Check
Scan to install
How to track compliance breaches to discover more
Netizen comments More
2221 HS code validation for diverse industries
2024-12-23 23:38 recommend
1332 Container freight index monitoring
2024-12-23 22:54 recommend
2396 Global trade corridor analysis
2024-12-23 21:59 recommend
231 HS code mapping for re-importation
2024-12-23 21:57 recommend
1954 Real-time supply chain event updates
2024-12-23 21:53 recommend